In my desire to help others from suffering some of the atrocious situations I have had to overcome as part of being a targeted individual, I am committed to explaining as much about them as I can in order to allow others avoiding suffering through them.
One of the most difficult arenas to navigate when you are a targeted individual is the absolute impunity with which government criminals commit cybercrimes against you. Everyone knows that the agency vested with investigating such crimes, the FBI, will not investigate or prosecute the crimes, even if you present them with actual evidence of the perpetrator.
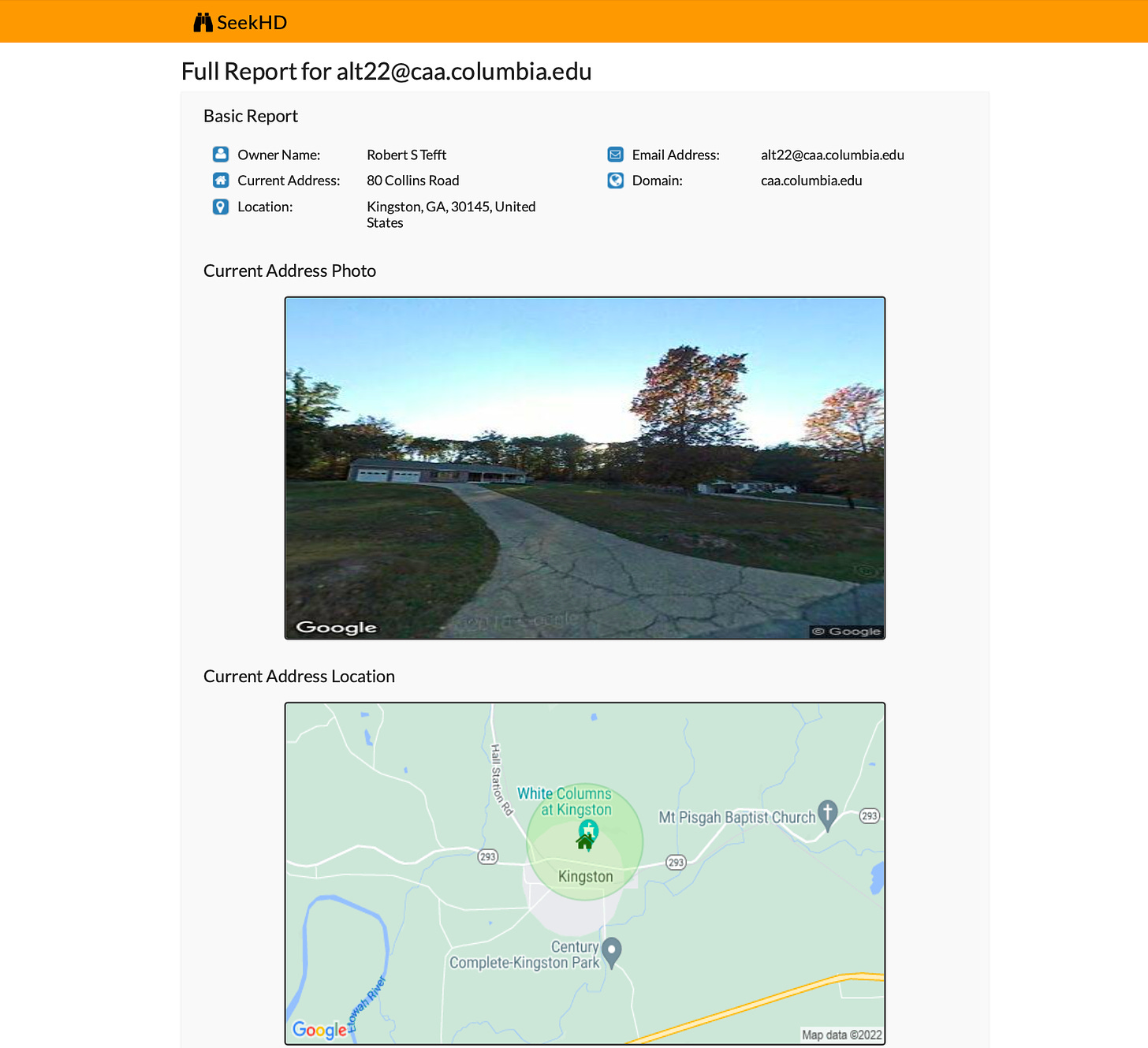
I filed a criminal complaint against the man that hacked my lifetime Columbia alumni email account almost two years ago. I even had evidence that when I sent an email, they sent themselves a copy of it. Instead of going to the ‘sent items’ folder, the copy of the email would go straight to the trash from where it would take them a couple of minutes to delete their bcc.
I am still waiting for the FBI to contact me about it. Not that I think they ever will do so voluntarily.
While we cannot force the FBI to do its job, there are things over which we definitely have control and the power to execute.
It is unrealistic to entirely avoid the illegal hacking perpetrated on our online accounts, but possible to somewhat protect them.
SOME BASIC PRECAUTIONS THAT CAN SAVE YOU A LOT OF ANGST AND LOSS RESULTING FROM BEING LOCKED OUT OF YOUR ONLINE ACCOUNTS.
While this post is not meant to be an exhaustive bag of tricks, the precautions I explain here may protect you from being permanently locked out of any of your accounts, as it happened to me.
SAVE PASSWORD? No!
For years, I would automatically save my online account passwords in my browsers. From the utilitarian ones like Amazon, to the confidential ones like email accounts, I automatically answered “YES” when the screen asked if I wanted to save the password.
DO NOT FALL FOR IT.
Keep a small notebook you zealously guard containing your handwritten passwords, secret questions and other information you need to access your accounts. When asked if you want to save your password, make an effort to type the password in the notepad of the computer, and then copy and paste it each time you will access that particular account.
When you save your password and do not force yourself to enter it, two things happen. First: you tend to forget it. If the criminals lock you out of your accounts, it will be very hard for you to recall them if you have not entered them in weeks or months.
Second: If you are not constantly entering your passwords, you will not notice when the criminals change them on you to lock you out of your accounts. If you are constantly entering your passwords and they change it in one or two accounts, you are likely to notice it, making it harder for them to make you wake up one day to have all your accounts out of your reach.
At all times assume that even though you DO NOT CONSENT, the government criminals and their minions know your passwords and access your accounts. Your goal as a TI is to not let them lock you out of them.
When the criminals pulled the rug from under my feet and locked me out of all my accounts in July of 2021, it took me months to recover 75% of them. Some of them I have never been able to recover because they changed the email on them or they were tied to my old phone number.
Others, like Microsoft, I could not recover for other reasons I set forth below.
MICROSOFT ACCOUNTS
Microsoft writes the software for the Fusion Centers. Need I say more?
For years, I had an outlook email that I was locked out of despite having the password. It contains confidential, attorney-client privileged documents and communications.
Microsoft has done everything to deny me access to my documents. The shenanigan they implemented to deprive me of access to the account (despite having the password) is stating that the login seems suspicious to them and that I have to submit a form with specific information from three emails I sent from that account, including recipient and exact subject matter.
I have been unable to come up with any of that information, particularly since the people to whom I wrote from that account will not provide the information I need to unlock it. Friends, colleagues and acquaintances from my past life are all in on my demise.
To prevent that the same tragedy happens to you if you have a Microsoft account, make it a habit to periodically cc or bcc yourself a copies of emails to another account, in case they play the same trick on you.
REFUSE AT ALL COSTS 2-STEP VERIFICATION.
Face it. The government criminals come in and out of your accounts with more ease than you do yourself. That is why the two-step verification is nothing but a trap for the criminals to prevent YOU from accessing your accounts.
When you have 2-step verification on, they easily block the text or the email where you get the code to access your account.
If your phone is lost or stolen, you will lose access to your accounts for a while. If you change your phone number without changing it first in that account, it is likely you will never access it again.
2-step verification may work well for non-TIs. For us second-class citizens with the most powerful hackers chasing our every cyberstep, it’s not only a waste of time but also a mechanism to lock us out of our accounts.
DO NOT CHANGE YOUR PHONE NUMBER: it’s a trap.
As TIs, many of us were mind-controlled to changing our phone number as a means to attempt escaping the hacking and surveillance. The problem is that the average adult has dozens of online accounts, many of which contain your phone number information. Some you seldom use, like government websites you visit once or twice a year.
If you change your phone number before deleting it from those sites, the criminals that follow your every step online will cause the website to send a 2-step verification to that number when you try to sign on again, even if you never activated it. You will likely be forever locked out of that account. Make sure that prior to cancelling a phone number, you change it in all the platforms you access.
SECURITY RECOVERY KEY? DO NOT FALL FOR IT.
Many platforms like Apple provide a security key for you to access your account in case you are locked out of it. Do not fall for it. It’s a trap. Upon downloading the key, the criminals change any of its digits, so that the key you think will work when you need it in reality will not. You will be forever locked out of the account trying to enter a security key that was adulterated from its inception without you realizing it.
PHONE APPS
Keep them to a minimum. Try as much as practicable to access email or online platforms through the phone’s web browser. Only keep one app open at a time. The criminals enter your phone through open apps you are not using to sabotage what you are trying to do, listen to or accomplish.
LITTLE VICTORIES
Discovering the information about the hacking my email account was a huge triumph that the criminals never saw coming.
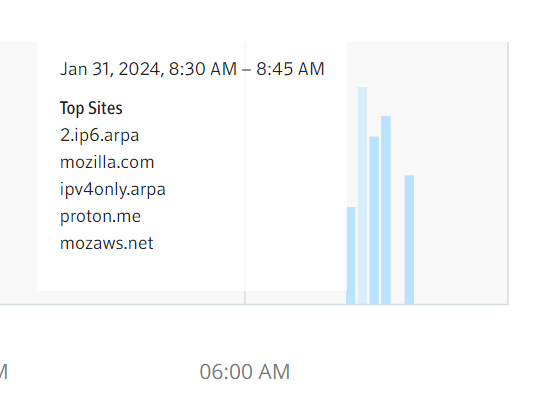
Discovering concrete evidence of DARPA’s illegal, unconsented presence in my router is another pearl in this otherwise tragic journey of being constantly spied upon.
These are two of the most damning examples that I have gathered during the past three years that prove that the criminals are powerful, but not in absolute control of their craft. Despite their state-of-the-art equipment, expertise, and seemingly limitless illegal access to your online accounts, sometimes they get careless and leave behind valuable tracks. Their incompetence allows us to gather evidence that will come in handy on the day we sit in front of a jury of our peers connecting the dots, telling the story of the illegal surveillance and persecution that those called to protect us put us through.
Do not forget that while being tortured is atrocious, our ability to document it in real time gives us the capacity to prepare for our day in court, when the judiciary finally accepts the fact that our plight is very real and not a ‘fantastical’ one.
Do not forget to keep a journal, and safely store away from your computer the evidence of the hacking that criminals carry out every day with absolute impunity.
Stay strong. We’ve got this.



Thanks Miss Ana! Very useful information! Thanks again for sharing!
Thank you